Author: Denis Avetisyan
A new study reveals effective strategies for detecting money laundering within stablecoin transactions on the Ethereum blockchain.
Carefully engineered behavioral features and tree ensemble models outperform deep learning techniques for identifying suspicious wallet activity.
Despite the increasing sophistication of illicit financial flows, stablecoins remain a critical transparency point for anti-money laundering (AML) efforts. This study, ‘StableAML: Machine Learning for Behavioral Wallet Detection in Stablecoin Anti-Money Laundering on Ethereum’, addresses this challenge by developing a robust framework for detecting illicit activity within Ethereum stablecoin transactions. Our analysis reveals that domain-informed tree ensemble models, leveraging carefully engineered behavioral features, significantly outperform graph neural networks in identifying complex money laundering typologies. Can this approach-prioritizing interpretable, high-precision detection-effectively balance regulatory compliance with the continued innovation of decentralized finance?
Decoding the Digital Flow: Unveiling Illicit Finance in the Modern Era
The proliferation of stablecoins, digital currencies designed to maintain a stable value relative to an asset like the US dollar, introduces novel complexities for Anti-Money Laundering (AML) compliance. Unlike traditional fiat currencies subject to stringent regulatory oversight and bank scrutiny, stablecoin transactions can occur with greater speed and across jurisdictional boundaries, potentially bypassing established detection mechanisms. This increased velocity and cross-border nature demand more sophisticated analytical techniques than those currently employed. Existing AML systems, often reliant on rule-based approaches and manual reviews, struggle to effectively monitor the intricate transaction patterns emerging within the stablecoin ecosystem. Consequently, financial institutions and regulatory bodies are actively exploring the implementation of advanced technologies – including machine learning and behavioral analytics – to identify and mitigate the risks associated with illicit financial flows channeled through these increasingly popular digital assets. The development of these techniques is crucial to preserving the integrity of the financial system and preventing the use of stablecoins for illegal purposes.
Current Anti-Money Laundering (AML) systems, largely built on rule-based approaches, are increasingly overwhelmed by the sheer volume and speed of modern financial transactions. The escalating complexity of these flows, driven by globalization and the rise of digital finance, generates a significant number of false positives – legitimate transactions flagged as suspicious – which strains resources and obscures genuine threats. This inability to efficiently process data not only increases operational costs for financial institutions but also creates opportunities for illicit actors to exploit the system, moving funds undetected amidst the noise. Consequently, a reliance on outdated methods results in missed risks and a diminished capacity to effectively combat financial crime, highlighting the urgent need for more sophisticated analytical tools.
Combating financial crime in the digital era demands a fundamental shift in how transaction monitoring is approached. Traditional rule-based systems, designed for slower, simpler financial flows, are increasingly inadequate against the speed and intricacy of modern transactions. Consequently, attention is turning towards data-driven methodologies, particularly those leveraging machine learning. These approaches move beyond static thresholds to identify subtle, complex patterns indicative of illicit activity-patterns that would otherwise go unnoticed. By analyzing vast datasets and adapting to evolving techniques, machine learning algorithms can dramatically improve detection rates while simultaneously reducing the burden of false positives, offering a more effective and efficient defense against the rising tide of digital financial crime.
The proliferation of digital assets, while offering innovative financial opportunities, simultaneously presents a significant challenge due to the anonymity afforded by certain cryptocurrencies and privacy-focused stablecoins. This characteristic facilitates the obfuscation of funds used in illicit activities, ranging from ransomware payments and terrorist financing to sanctions evasion and money laundering. Traditional financial tracking methods are often ineffective against these decentralized systems, requiring the development of sophisticated analytical tools capable of de-anonymizing transactions and identifying suspicious patterns. These tools leverage advanced techniques like blockchain analysis, network visualization, and machine learning to trace the flow of funds, pinpoint actors involved in illegal activities, and ultimately disrupt the financial infrastructure supporting criminal enterprises. The increasing sophistication of these illicit financial flows necessitates a continuous evolution of analytical capabilities to maintain effective oversight and mitigate the risks posed by anonymity in the digital age.
Constructing Insight: Feature Engineering and Model Architecture
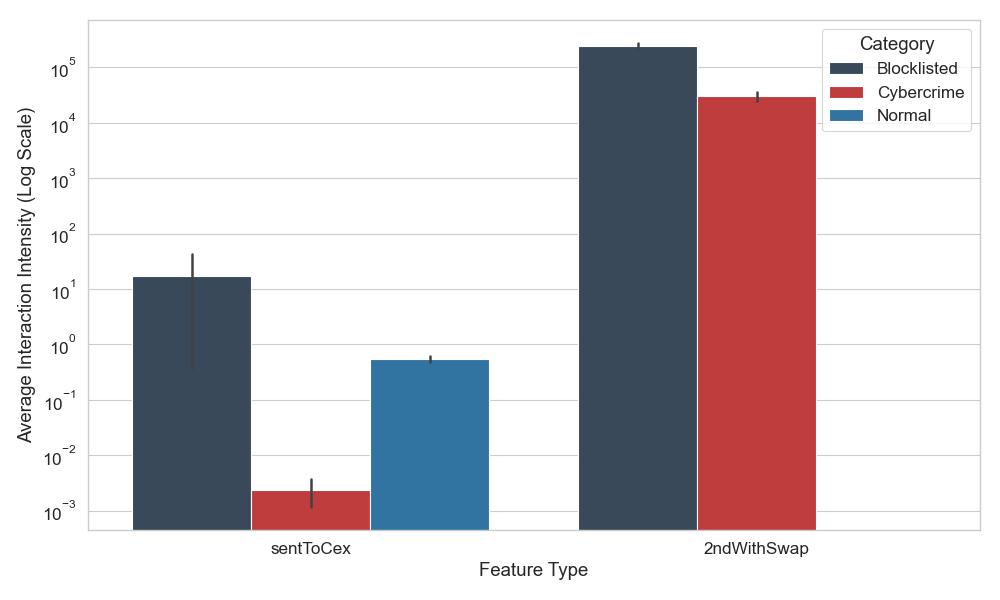
The feature engineering process involved constructing 68 domain-specific attributes derived from stablecoin transaction data. These features were categorized into four primary groups: Interaction features, capturing relationships between wallets; Derived Network features, calculated from the transaction graph; Transfer-based features, quantifying characteristics of individual transactions; and Temporal/Direct features, representing time-based or immediately observable attributes. This categorization facilitated a systematic approach to feature creation and allowed for focused analysis of different aspects of on-chain activity. The resulting feature set was designed to provide a comprehensive representation of wallet behavior and transaction patterns for use in subsequent model training and evaluation.
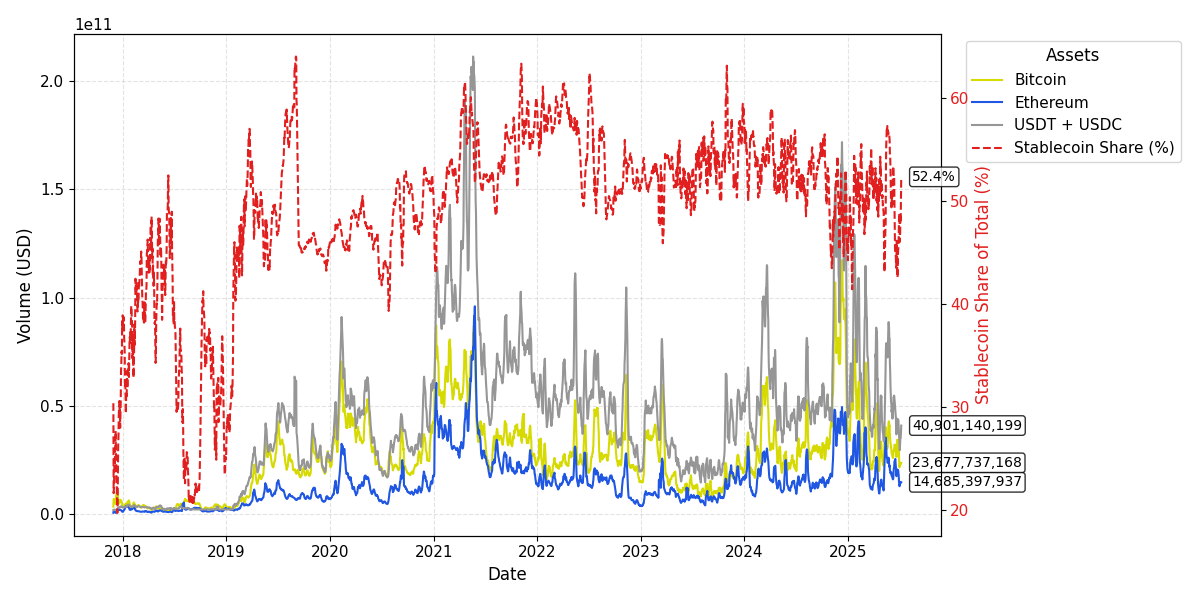
The StableAML Dataset serves as the primary training resource for our machine learning models, comprising a large-scale collection of data specifically focused on stablecoin transactions. This dataset includes transaction records, wallet addresses, and associated metadata, enabling the analysis of on-chain activity related to stablecoins. The scale of the dataset, encompassing a significant volume of transactions and unique addresses, allows for robust model training and evaluation. Data is sourced from multiple blockchain networks and undergoes a rigorous cleaning and validation process to ensure data quality and consistency, ultimately providing a reliable foundation for identifying patterns and anomalies in stablecoin flows.
A diverse set of machine learning models was implemented and assessed to determine optimal performance on the stablecoin flow analysis task. These included Logistic Regression, providing a baseline linear model; tree-based ensemble methods such as Random Forest, XGBoost, LightGBM, and CatBoost, known for their robustness and feature importance capabilities; a Deep Neural Network, leveraging multi-layer perceptrons for complex pattern recognition; and a Graph Neural Network, specifically utilizing the GraphSAGE algorithm to incorporate network structure into the model. Performance metrics were recorded for each model to facilitate comparative analysis and model selection.
The Graph Neural Network (GNN) implemented in this system employs the GraphSAGE algorithm to directly incorporate network topology into the learning process. Unlike traditional machine learning models which treat wallets and transactions as isolated data points, the GNN represents them as nodes and edges within a graph. GraphSAGE then learns node embeddings by aggregating feature information from a node’s immediate neighbors, enabling the model to capture complex relationships and dependencies between wallets and the transactions they participate in. This approach allows the GNN to infer characteristics of wallets and transactions based on their position and connections within the larger network, offering a more nuanced understanding than models relying solely on individual feature sets.

Validating Detection Accuracy: Performance and Measurement
The Macro-F1 score was employed as the primary performance metric to assess model accuracy in identifying suspicious transactions. This statistic calculates the harmonic mean of precision and recall, but crucially, it does so by averaging these metrics across all risk categories before calculating the final F1 score. This approach ensures that the metric is not biased towards the majority class and provides a balanced evaluation of performance across all categories, regardless of their prevalence in the dataset. A higher Macro-F1 score indicates a better overall balance between identifying true positives and minimizing both false positives and false negatives across all risk levels.
Evaluation of model performance indicated a substantial improvement in detection accuracy when utilizing machine learning approaches compared to traditional rule-based systems. Specifically, the machine learning models achieved a Macro-F1 score of 0.999. The Macro-F1 score calculates the unweighted mean of the precision and recall for each risk category, providing a balanced measure of overall performance. This result demonstrates a significant capability to accurately identify suspicious transactions with a high degree of both precision and recall across all defined risk levels, exceeding the capabilities of rule-based systems.
Evaluation of model performance indicates that tree ensemble methods achieved a Macro-F1 score ranging from 0.975 to 0.979. This performance level represents a substantial improvement over Deep Learning approaches, which yielded Macro-F1 scores between 0.80 and 0.87 under the same testing conditions. The Macro-F1 score, calculated across all risk categories, provides a balanced measure of both precision and recall, highlighting the superior ability of tree ensembles to accurately identify suspicious transactions compared to the tested Deep Learning models.
The Graph Neural Network (GNN) demonstrated consistently high performance, achieving an Area Under the Receiver Operating Characteristic curve (AUROC) exceeding 0.997, which indicates a strong capacity to discriminate between suspicious and non-suspicious transactions. Complementing this, the CatBoost model exhibited a Recall score of 0.95 specifically for the ‘Blocklisted’ class, representing a substantial improvement over the Recall rates achieved by other evaluated models for identifying transactions associated with known blocked entities. These results indicate both the GNN’s overall discriminatory power and CatBoost’s effectiveness in minimizing false negatives within a critical risk category.
Strengthening Financial Security: Implications and Future Trajectory
The convergence of blockchain analytics and machine learning is revolutionizing the fight against financial crime and the enforcement of regulatory standards. Blockchain’s immutable record of transactions, when subjected to advanced analytical techniques, reveals patterns and anomalies indicative of illicit activity that would otherwise remain hidden. Machine learning algorithms excel at sifting through the vast quantities of blockchain data, identifying subtle connections and predicting potentially fraudulent behavior with increasing accuracy. This proactive approach moves beyond reactive investigations, enabling financial institutions and regulatory bodies to preemptively address risks associated with money laundering, terrorist financing, and other illegal activities, ultimately bolstering the integrity of the financial system and ensuring greater compliance with evolving regulations.
Recent investigations reveal that data-driven methodologies hold considerable promise in the ongoing battle against illicit financial activities. This research highlights a shift from reactive investigations – responding to crimes after they occur – to proactive risk mitigation, leveraging the power of analytics to identify potentially harmful transactions before they are completed. By analyzing patterns and anomalies within financial data, these approaches enable the preemptive flagging of suspicious activity, bolstering anti-money laundering (AML) efforts and counter-terrorism financing initiatives. The capacity to anticipate and neutralize financial crimes, rather than simply reacting to their consequences, represents a significant advancement in financial security and regulatory compliance, offering a more robust defense against evolving threats.
The automation of suspicious transaction detection represents a significant advancement in anti-money laundering (AML) operations, offering the potential to substantially alleviate the workload currently shouldered by human analysts. Traditional AML processes heavily rely on manual review of flagged transactions, a resource-intensive and time-consuming undertaking prone to human error and alert fatigue. By employing machine learning algorithms to proactively identify patterns indicative of illicit financial activity, systems can filter out a large volume of false positives, presenting analysts with a significantly smaller, more focused set of potentially fraudulent transactions. This not only accelerates the investigation process but also enables analysts to dedicate their expertise to complex cases requiring nuanced judgment, ultimately bolstering the overall efficiency and effectiveness of financial crime prevention efforts.
Continued development centers on significantly broadening the scope of data utilized in these analytical models, moving beyond current transaction histories to incorporate a wider range of contextual features – such as network analysis of wallet interactions and behavioral patterns indicative of risk. Researchers are also investigating the application of cutting-edge machine learning methodologies, including graph neural networks and federated learning, to not only improve the precision of anomaly detection but also to bolster the system’s robustness against evolving evasion tactics. This iterative process of data enrichment and algorithmic refinement aims to create a more proactive and resilient financial security infrastructure, capable of adapting to the increasingly sophisticated landscape of illicit finance and maintaining the integrity of global financial systems.
The pursuit of robust systems for detecting illicit financial flows, as explored in this study of stablecoin transactions, echoes a fundamental principle of structural integrity. The research demonstrates how feature engineering, focusing on network-level behavioral patterns, provides a surprisingly effective foundation for identifying anomalies. This aligns with the observation that systems break along invisible boundaries – if you can’t see them, pain is coming. As Blaise Pascal noted, “The eloquence of the body is in its gestures.” Similarly, the ‘gestures’ of blockchain transactions – the patterns of interaction within the network – reveal far more than isolated data points, providing critical signals for effective monitoring and ultimately, a more resilient financial ecosystem.
The Road Ahead
The demonstrated efficacy of feature engineering, coupled with tree ensembles, in discerning illicit activity within stablecoin transactions presents a curious paradox. The pursuit of increasingly complex models, often lauded for their representational power, yielded diminishing returns. This suggests a fundamental truth: elegance, not sheer computational capacity, governs effective system analysis. Every new dependency – a deeper neural network layer, a more intricate feature transformation – is the hidden cost of freedom, introducing opacity and potential for unforeseen failure.
Future work must address the limitations inherent in any static feature set. The adversarial nature of money laundering ensures that behavioral patterns will evolve, demanding adaptive feature engineering or, perhaps, a return to first principles – a deeper understanding of the underlying economic incentives that drive illicit transactions. Graph neural networks, while promising, require substantial refinement to avoid overfitting and maintain interpretability.
Ultimately, the challenge lies not merely in detecting anomalies, but in constructing a holistic model of legitimate economic activity. Structure dictates behavior; a complete understanding of the network’s natural state is prerequisite to identifying deviations. This necessitates a move beyond purely transaction-focused analysis towards incorporating off-chain data and contextual information, acknowledging that the blockchain is merely a reflection of a larger, more complex reality.
Original article: https://arxiv.org/pdf/2602.17842.pdf
Contact the author: https://www.linkedin.com/in/avetisyan/
See also:
- Invincible Season 4 Gender Swaps Tech Jacket As Fans Question Major Comic Change
- Building Agents That Learn and Improve Themselves
- Gold Rate Forecast
- Silver Rate Forecast
- Games That Faced Bans in Countries Over Political Themes
- Trading Crypto with AI: A New Approach to Portfolio Management
- Superman Flops Financially: $350M Budget, Still No Profit (Scoop Confirmed)
- 22 Films Where the White Protagonist Is Canonically the Sidekick to a Black Lead
- Unveiling the Schwab U.S. Dividend Equity ETF: A Portent of Financial Growth
- 15 Films That Were Shot Entirely on Phones
2026-02-23 12:10