Unveiling Information’s Hidden Pathways
![The function [latex] g_{\alpha}(x,r) = \ln_{1/\alpha} r(x) [/latex] defines a relationship between a variable <i>r</i> and <i>x</i>, scaled by a parameter α, establishing a logarithmic connection crucial for characterizing the system’s behavior.](https://arxiv.org/html/2601.09406v1/x1.png)
A new framework clarifies the meaning of alpha-mutual information by connecting it to the fundamental concept of information leakage.
![The function [latex] g_{\alpha}(x,r) = \ln_{1/\alpha} r(x) [/latex] defines a relationship between a variable <i>r</i> and <i>x</i>, scaled by a parameter α, establishing a logarithmic connection crucial for characterizing the system’s behavior.](https://arxiv.org/html/2601.09406v1/x1.png)
A new framework clarifies the meaning of alpha-mutual information by connecting it to the fundamental concept of information leakage.
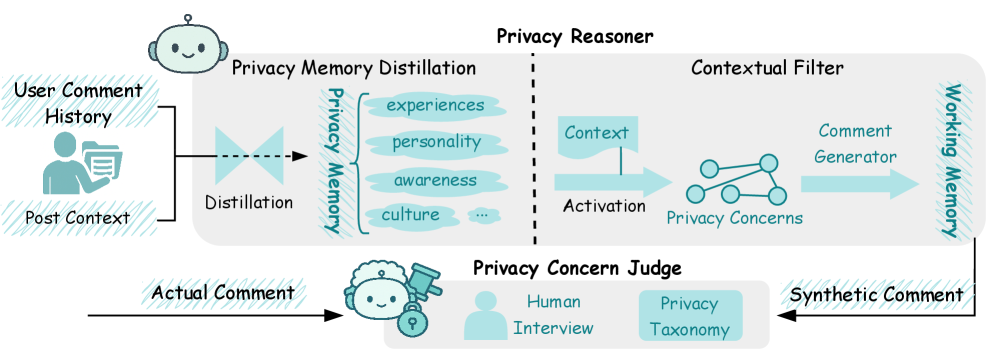
Researchers have developed an AI agent that attempts to model human privacy reasoning, predicting how individuals will react to different privacy-related scenarios.
New research reveals a surprisingly effective method for eliminating orientation-induced biases in vision-language and image generation models, leading to fairer and more robust AI.
Researchers have developed a novel framework that significantly improves the detection of manipulated images, even when those images come from unfamiliar sources.
A new approach leverages the power of artificial intelligence to accurately forecast how galaxies will interact, offering insights into cosmic evolution.
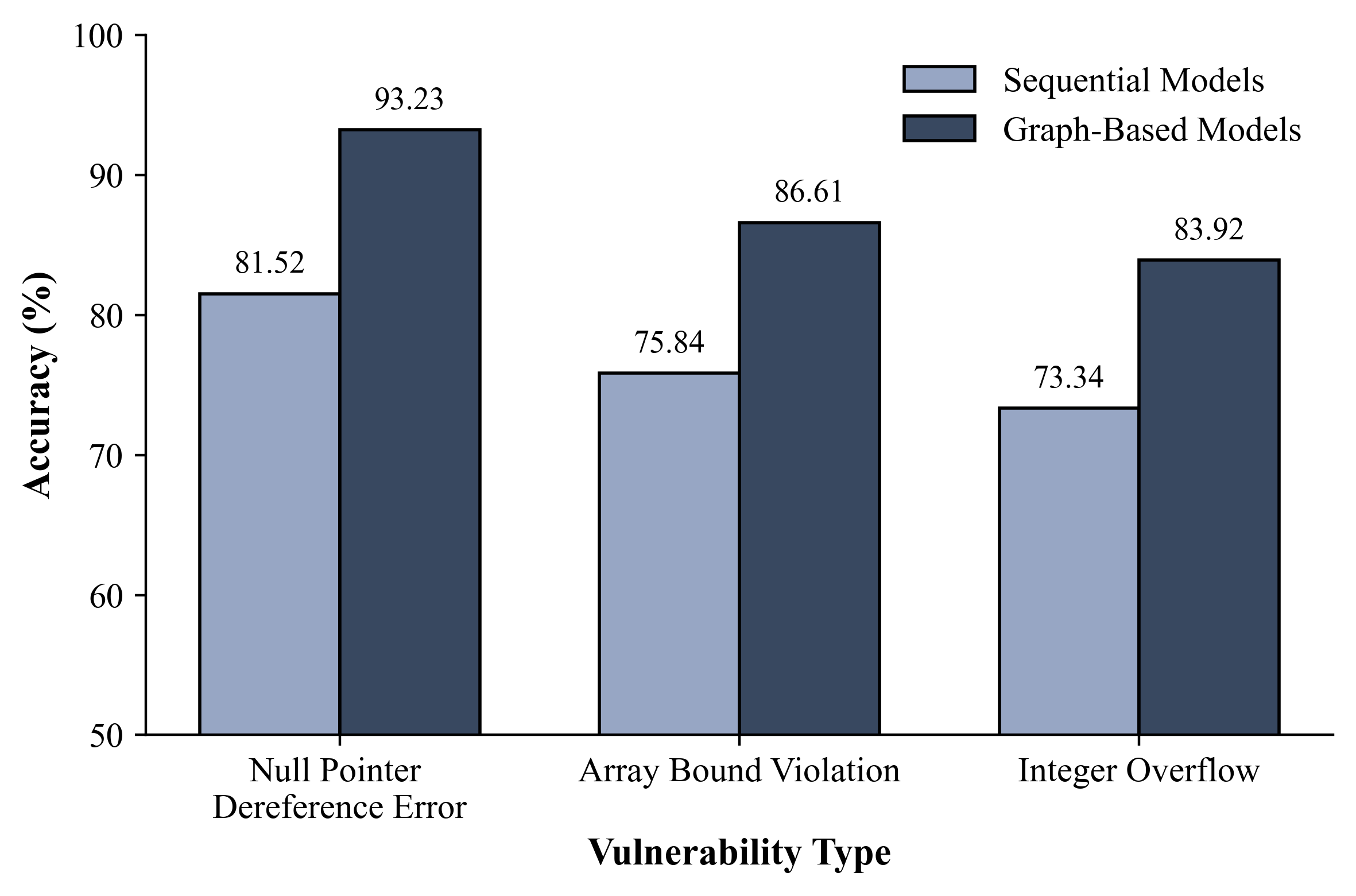
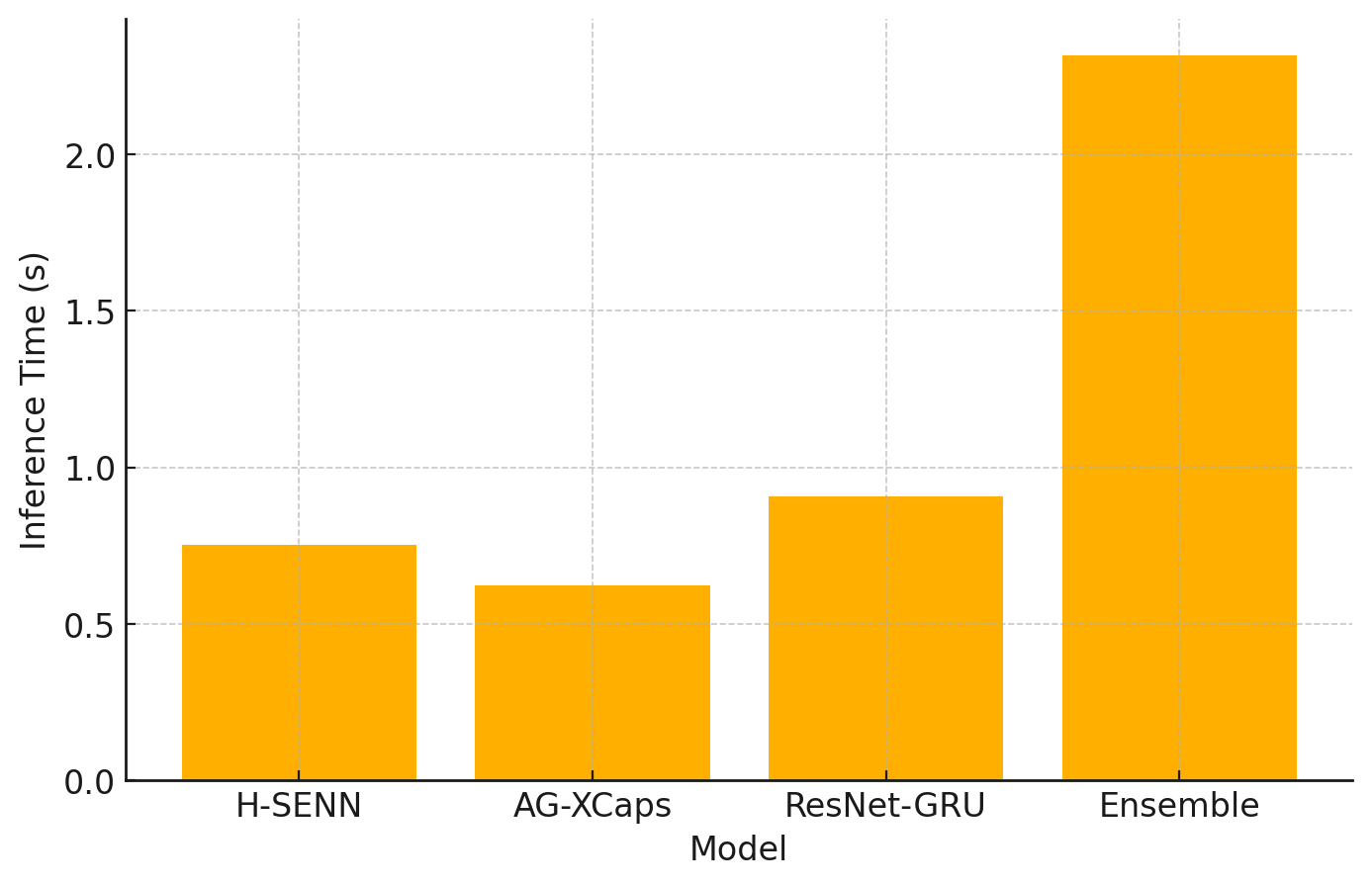
A new approach leverages deep learning to directly analyze x86-64 machine code, offering a streamlined path to identifying security flaws.
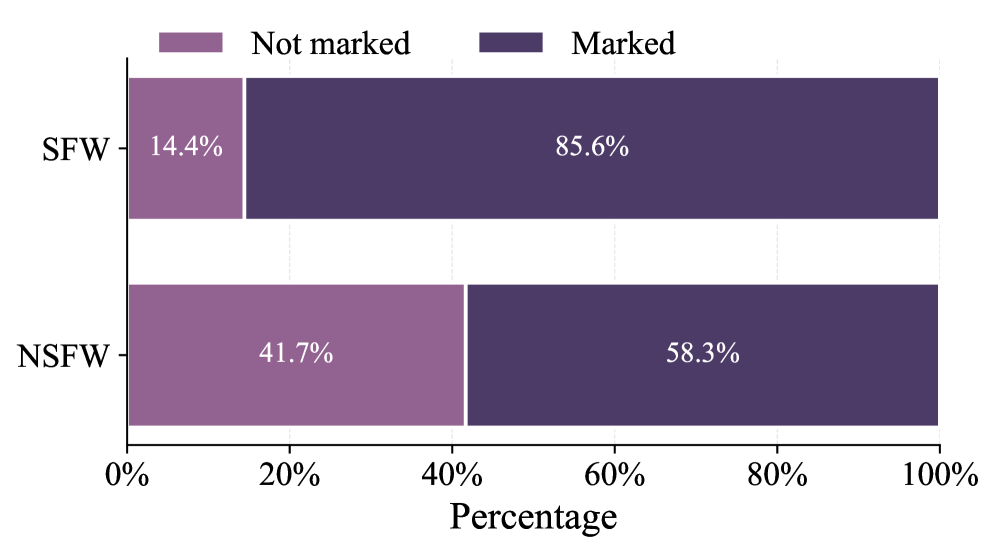
A new study examines the Civitai platform and its bounty system, revealing a thriving market for AI-generated adult content and the challenges of moderating this rapidly expanding landscape.

Researchers have created a new dataset and methodology to better identify when artificial intelligence systems are dodging difficult questions in the realm of financial queries.

Researchers are leveraging the power of generative adversarial networks and long short-term memory networks to improve the accuracy and reliability of identifying unusual energy consumption patterns.

A new study investigates whether modern computer vision techniques, specifically Vision Transformers and Convolutional Neural Networks, can accurately identify motifs on ancient Roman coins.