Author: Denis Avetisyan
Researchers have developed a novel system that combines intelligent program analysis with large language models to dramatically improve the detection of malware created by artificial intelligence.
CogniCrypt leverages LLM-guided concolic execution to prioritize paths and classify vulnerabilities in AI-generated polymorphic malware, exceeding the performance of existing detection methods.
Conventional malware detection relies on identifying known signatures, a strategy increasingly ineffective against the polymorphic and context-aware threats emerging from automated malware generation. This paper introduces ‘Synergistic Directed Execution and LLM-Driven Analysis for Zero-Day AI-Generated Malware Detection’, a novel framework, CogniCrypt, that synergistically combines Large Language Model (LLM)-guided concolic execution with deep learning for provably sound and relatively complete zero-day threat detection. Experimental results demonstrate CogniCrypt achieves up to 52.2 percentage point improvements over state-of-the-art baselines on AI-generated malware, exceeding 97% accuracy-but can this approach adapt to the rapidly evolving landscape of LLM-synthesized malicious code?
The Shifting Sands of Malware: A New Threat Landscape
Conventional malware detection relies heavily on identifying specific code signatures – unique fingerprints of known malicious software. However, a growing class of threats, termed polymorphic malware, actively evades this approach by continuously modifying its code while retaining its core functionality. This constant alteration renders static signatures obsolete, as the malware’s appearance changes with each iteration, effectively camouflaging itself from signature-based systems. The sophistication lies not in novel malicious actions, but in the ability to consistently present a different facade, demanding security solutions that move beyond simple pattern matching and focus on behavioral analysis to identify malicious intent regardless of the code’s external form.
The proliferation of artificial intelligence is extending beyond beneficial applications and into the realm of cybersecurity threats. Modern malware is no longer solely crafted by human programmers; instead, malicious code can now be autonomously generated and refined by AI algorithms. This introduces a significant challenge for traditional security systems, as AI-generated malware exhibits a capacity for rapid mutation and polymorphic behavior that easily evades signature-based detection. Consequently, static defenses are proving insufficient; adaptive detection methods-those capable of learning, predicting, and responding to novel threats-are crucial. These systems must move beyond recognizing known malicious patterns and instead focus on identifying anomalous behavior and intent, effectively anticipating and neutralizing attacks before they can fully deploy. The speed and sophistication of AI-driven malware demand a dynamic, intelligent defense capable of matching-and ultimately surpassing-the capabilities of the adversary.
The escalating sophistication of modern malware demands a fundamental change in cybersecurity strategy, moving beyond the limitations of signature-based detection. Traditional methods, reliant on identifying known malicious code, are increasingly ineffective against threats that dynamically alter their characteristics. Recent research demonstrates the efficacy of proactive approaches, notably with CogniCrypt, a system engineered to anticipate malicious intent. Evaluations reveal CogniCrypt achieves an impressive 97.5% accuracy in identifying AI-generated malware – representing a substantial 19.3-52.2 percentage point improvement over currently deployed detection technologies. This leap in performance suggests a viable pathway toward a more resilient security posture, one focused on predicting and neutralizing threats before they can inflict damage.

Intelligent Path Exploration: The Core of CogniCrypt
Concolic execution, the foundation of CogniCrypt’s path exploration, operates by simultaneously executing a program with concrete inputs and maintaining symbolic representations of program variables. This dual approach allows the framework to explore program paths while tracking the constraints that led to each execution state. Concrete execution provides immediate results and identifies feasible paths, while symbolic execution enables the system to reason about the program’s logic and generate new inputs that satisfy specific constraints, effectively expanding path coverage beyond what traditional dynamic analysis methods can achieve. By combining these techniques, CogniCrypt can systematically explore the program’s state space and identify potentially malicious code paths.
CogniCrypt addresses the scalability limitations of concolic execution, specifically the ‘Path Explosion Problem’, by integrating Large Language Models (LLMs) into the path exploration process. Traditional concolic execution explores program states in a largely undirected manner, leading to exponential growth in the number of paths examined. CogniCrypt’s LLM component functions as a heuristic guide, analyzing program state and predicting the likelihood of a given path containing malicious code. This allows the system to prioritize exploration along potentially harmful routes, significantly reducing the total number of paths required to achieve meaningful code coverage and identify vulnerabilities.
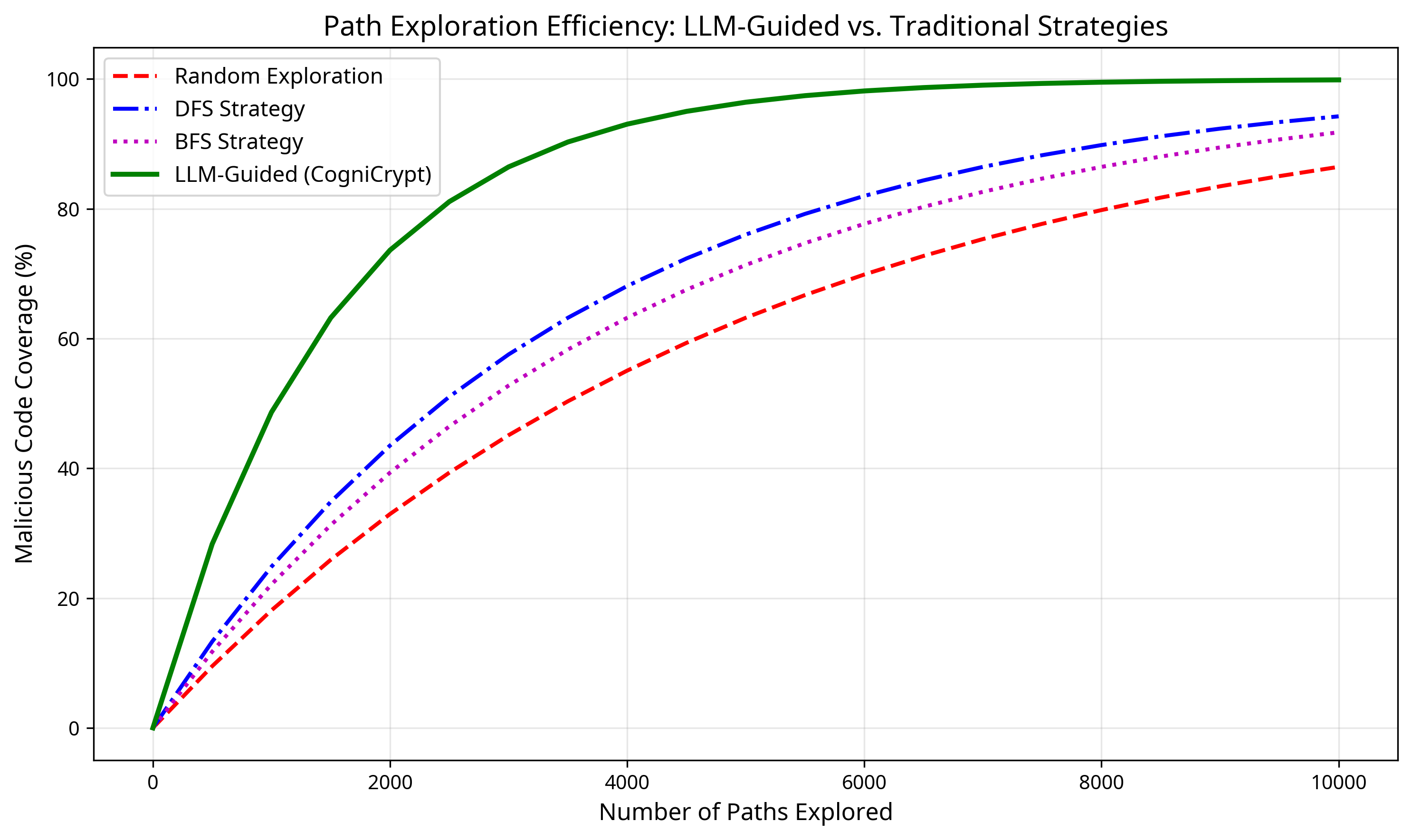
CogniCrypt’s path prioritization leverages a ‘Path Priority Function’ integrated within a Large Language Model (LLM) to optimize program state space traversal. This function assesses the likelihood of a given execution path leading to malicious code, allowing the LLM to guide exploration towards potentially harmful areas with greater efficiency. Empirical results demonstrate significant reductions in path count required for malicious code coverage; CogniCrypt achieves comparable coverage to traditional Depth-First Search (DFS) and Breadth-First Search (BFS) using 73.2% and 68.5% fewer paths, respectively. This reduction in explored paths directly translates to decreased computational cost and improved scalability for dynamic analysis.
CogniCrypt’s core functionality relies on the angr framework for concolic execution and the Z3 theorem prover for constraint solving. Angr facilitates the dynamic analysis process by simultaneously executing concrete code paths and maintaining symbolic representations of program variables. When a branch is encountered, Z3 is invoked to solve constraints derived from the symbolic state, determining the input conditions required to reach different execution paths. The integration of angr and Z3 provides a robust and automated platform for exploring program behavior and identifying potential vulnerabilities, forming the foundation upon which CogniCrypt’s LLM-guided path prioritization is built.

Decoding Intent: Transformer-Based Malware Classification
CogniCrypt employs a Transformer-Based Path Constraint Classifier to quantify the maliciousness of software by analyzing symbolic execution traces. This classifier processes ‘Path Constraints’ – logical expressions defining the conditions for specific program execution paths – and maps these constraints to a numerical score indicating the likelihood of malicious behavior. The system utilizes symbolic execution to generate these path constraints, representing the program’s logic in a format suitable for machine learning analysis. The resulting maliciousness score is then used to categorize and prioritize potential threats, enabling a more efficient and accurate malware detection process. This approach allows CogniCrypt to identify malicious intent based on program behavior rather than relying solely on signature-based detection methods.
The malware classification component within CogniCrypt is implemented using the PyTorch deep learning framework, enabling GPU acceleration and dynamic computation graphs. To improve classification accuracy and reduce training time, the system leverages pre-trained models sourced from the Hugging Face Transformers library. These models, initially trained on large text corpora, provide a strong foundation for feature extraction from symbolic execution traces, which are then fine-tuned with malware-specific datasets. This transfer learning approach significantly enhances performance compared to training a model from scratch, particularly in scenarios with limited labeled malware samples. The use of pre-trained models also allows for rapid prototyping and experimentation with different architectures.
The CogniCrypt malware classification system utilizes path constraints – logical formulas representing the conditions that must be met for a program to follow a specific execution path – as a key feature for identifying malicious behavior. These constraints, typically expressed in propositional logic, are derived during symbolic execution and detail conditional statements and variable relationships. Analysis focuses on identifying patterns within these formulas that correlate with known malware techniques, such as attempts to bypass security checks, manipulate system resources, or establish network connections. The presence of constraints indicative of these actions contributes to a higher maliciousness score, allowing the system to flag potentially harmful code.
The Transformer-Based Path Constraint Classifier within CogniCrypt utilizes a reinforcement learning (RL) feedback loop to continuously improve its maliciousness scoring accuracy. This loop operates by evaluating the classifier’s prioritization of path constraints during symbolic execution. The RL agent receives a reward signal based on the correctness of the resulting maliciousness score – higher rewards are given for accurate classifications. This reward signal is then used to adjust the Large Language Model’s (LLM) prioritization policy, influencing which path constraints are examined more closely in subsequent analyses. Through iterative refinement via this feedback loop, the classifier learns to focus on the most relevant features within path constraints, thereby increasing the efficiency and precision of malware detection.

Beyond Detection: Validation and Broader Implications
A core strength of CogniCrypt lies in its rigorous soundness, a characteristic designed to drastically reduce false positives in malware detection. This isn’t simply about identifying potential threats, but definitively confirming malicious intent before flagging a file or process. The framework achieves this through a combination of formal verification techniques and runtime analysis, ensuring that every flagged instance represents a genuine security risk. This level of certainty is critical; false alarms can disrupt legitimate operations, erode trust in security systems, and overwhelm security personnel. By prioritizing accuracy, CogniCrypt offers a reliable defense, minimizing unnecessary interventions and focusing resources on confirmed threats, ultimately contributing to a more stable and secure computing environment.
CogniCrypt is designed not to achieve absolute, and often impractical, detection of all possible malicious code paths, but rather to prioritize ‘Relative Completeness’. This pragmatic approach acknowledges the limitations of computational resources and focuses on identifying all reachable malicious pathways within a defined budget. By concentrating on realistically exploitable threats – those a potential attacker could actually trigger – the framework maximizes its effectiveness. This differs from exhaustive analysis, which can become bogged down in irrelevant or inaccessible code, and instead delivers a robust defense against active threats while remaining computationally feasible, even as malware complexity increases.
Rigorous testing of CogniCrypt against the ‘AI-Gen-Malware Dataset’ confirms its robust performance in identifying contemporary threats. This dataset, comprised of malicious code generated by artificial intelligence, presents a uniquely challenging landscape for traditional security systems. CogniCrypt not only met this challenge but excelled, achieving an Area Under the Receiver Operating Characteristic curve (AUC-ROC) of 0.993. This near-perfect score indicates an exceptional ability to accurately distinguish between benign and malicious code, even when faced with novel malware strains crafted to evade conventional detection methods. The result highlights CogniCrypt’s potential to provide a crucial defense against the rapidly evolving threat of AI-powered malware.
Traditional malware detection relies heavily on signature-based methods, identifying threats by matching known patterns – a reactive approach vulnerable to new and polymorphic malware. CogniCrypt diverges from this paradigm by analyzing the behavior of code, rather than simply seeking pre-defined signatures. This behavioral analysis allows the system to identify malicious intent even in previously unseen malware, offering a proactive defense against rapidly evolving threats. By focusing on the underlying computational logic, rather than static characteristics, CogniCrypt establishes a robust foundation for future security innovations, potentially extending beyond malware detection to encompass broader cybersecurity challenges and adaptive threat response systems.

CogniCrypt’s architecture embodies a reductionist principle. The framework distills the complexities of AI-generated malware analysis into prioritized execution paths, guided by the LLM’s understanding of malicious intent. This focus on essential pathways mirrors a core tenet of efficient problem-solving. As Carl Friedrich Gauss observed, “If I have seen further it is by standing on the shoulders of giants.” CogniCrypt doesn’t attempt to reinvent symbolic execution; rather, it leverages the power of LLMs to intelligently prioritize exploration – building upon established techniques to achieve a more refined and effective system for vulnerability classification and polymorphic malware detection. Clarity is the minimum viable kindness.
Further Lines of Inquiry
The presented work addresses a symptom, not the disease. CogniCrypt improves detection, certainly, but assumes the adversary continues to operate within predictable boundaries of algorithmic generation. Future effort must consider methods to anticipate novel generative strategies, those that deliberately evade pattern-based analysis. The true challenge lies not in identifying what is, but in predicting what will be generated.
Current path prioritization relies heavily on reinforcement learning, a process inherently sensitive to the training data. The framework’s efficacy is thus tethered to the quality and representativeness of the malware corpus used. Research should investigate methods for continual learning, or transfer learning from disparate security domains, to mitigate the risk of brittle generalization. A perfect detector, built on imperfect data, remains an illusion.
The integration of LLMs introduces an interesting dependency. The models’ reasoning, though demonstrably useful, is opaque. Understanding why a particular path is deemed more likely to contain malicious code is crucial. Future work should explore explainable AI techniques, not to justify the system’s decisions, but to reveal the underlying vulnerabilities the malware exploits. Clarity, even in the face of complexity, is paramount.
Original article: https://arxiv.org/pdf/2603.09044.pdf
Contact the author: https://www.linkedin.com/in/avetisyan/
See also:
- Building 3D Worlds from Words: Is Reinforcement Learning the Key?
- Spotting the Loops in Autonomous Systems
- The Best Directors of 2025
- The Glitch in the Machine: Spotting AI-Generated Images Beyond the Obvious
- 2025 Crypto Wallets: Secure, Smart, and Surprisingly Simple!
- Umamusume: Gold Ship build guide
- 20 Best TV Shows Featuring All-White Casts You Should See
- Mel Gibson, 69, and Rosalind Ross, 35, Call It Quits After Nearly a Decade: “It’s Sad To End This Chapter in our Lives”
- Gold Rate Forecast
- Uncovering Hidden Signals in Finance with AI
2026-03-12 04:55